Our project has reached the end of its lifetime this November, having had the opportunity to create a DevSecOps momentum that has brought us new open source technology tools and research paths to face a forthcoming heterogeneous and highly technological future. PIACERE already allows to access an integrated DevSecOps framework to develop, verify, release, configure, provision, and monitor Infrastructure as Code (IaC).
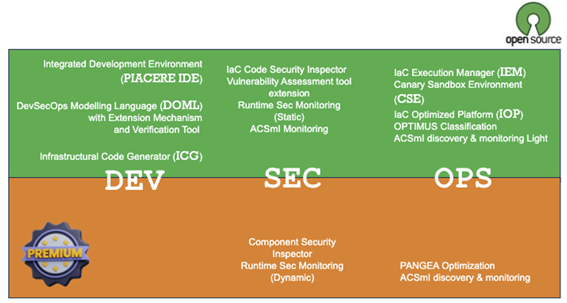
The first of seven Key Exploitable Results (KERs) of PIACERE is the full stack technology (Horizon Results Platform 64863), that provides a toolbox accessible through an Eclipse-based Integrated Development Environment (IDE), supporting the PIACERE’s novel framework for modelling application deployment, modelling infrastructure applications and refactoring possibilities. It acts on Dev, Sec and Ops with six KERs building on 25 intelectual property results, most of which with permissive open-source licenses as Apache 2.0 or MPL 2.0.
The consolidated business plans of this project show how PIACERE’s nature is dedicated to Open Research, with a large number of publications exposed in green and gold access, a white paper submitted to the Open Research Europe initiative, and a sustainability strategy relying on five pillars of Open Research Community Engagement as published in the public deliverable D8.6 dedicated to the dissemination and communication of the project.
The Open PIACERE, the OSS version of the PIACERE technology, is an important outcome of the exploitation workforce in this reporting period, based on the IPR management, KER analysis and strategy planning for the value proposition of the open source technology in PIACERE, greatly supporting the Community Engagement.
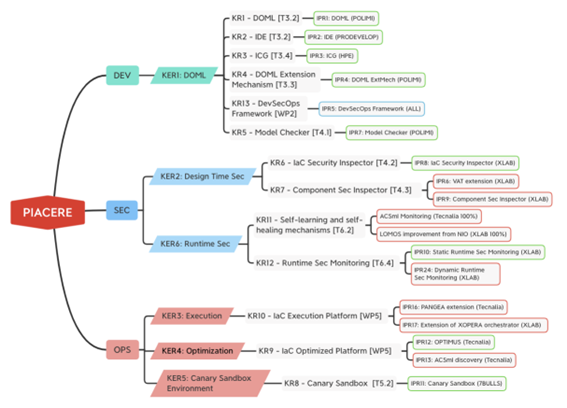
The first KER of the project – DOML (HRP 44131) – improves the ability of (non-)expert DevSecOps teams to model provisioning, deployment and configuration needs in complex contexts by providing a set of abstractions of execution environments and composing them into machine-readable representations. DOML and ICG allow DevSecOps teams to select and combine the abstractions with the purpose of creating a correct infrastructure provisioning, configuration management, deployment and self-healing model.
PIACERE’s approach to design time security (HRP 44193) helps regain trust in IaC through the DOML verification and the automation of IaC code quality checking for errors and vulnerable dependencies, and thus improving IaC integrity and applicability. It enables users to optimize and reduce the number of errors in their deployment procedure, decreasing the time needed to detect IaC malfunctioning or changes in the working conditions of the generated IaC at execution time.
At runtime, the approach ensures that the conditions of the QoS are met at all times and that a failure or non-compliance of NFRs is not likely to occur, with verified security violations at runtime. PIACERE’s intelligent Runtime Security (HRP 64861) includes a monitoring system capable of detecting security-related events and incidents in the deployed application’s environment. It is (to the extent possible) deployable automatically and notifies users about security alerts.
The IaC Execution Manager (HRP 44197) will then help develop and maintain IaC for heterogeneous infrastructures and different phases (configure, provision, deploy, orchestrate), supporting multilingualism with one tool. This result allows for automatic, parametrizable, and therefore faster and easier execution, orchestration and deployment of IaC code on heterogeneous vendor providers. It has no need to utilize different languages for the different providers, and it facilitates the exploitation of the project with independence to the provider.
The IaC Optimisation Platform (HRP 64853) will then perform the most appropriate deployment configurations that best meet your defined constraints out of DevSecOps catalogue of services, resources and infrastructural elements by means of optimization algorithms. It builds on well-known libraries, such as jHipster and jMetal, and is provided to the user in a ranked way, in order to chose the option that fits better to user needs.
PIACERE includes also an innovative Canary Sandbox Environment (HRP 64859) that allows unit testing of the behaviour of the infrastructural code on an isolated environment, which would enable the simulation of conditions for the production environment and identify some of the most common anti-patterns. Currently there is no out of the box solution to make a test deployment, with real infrastructure deployment, but in the sandbox (controlled) environment.

0 Comments